Zero Trust Security Model Explained with Use Cases
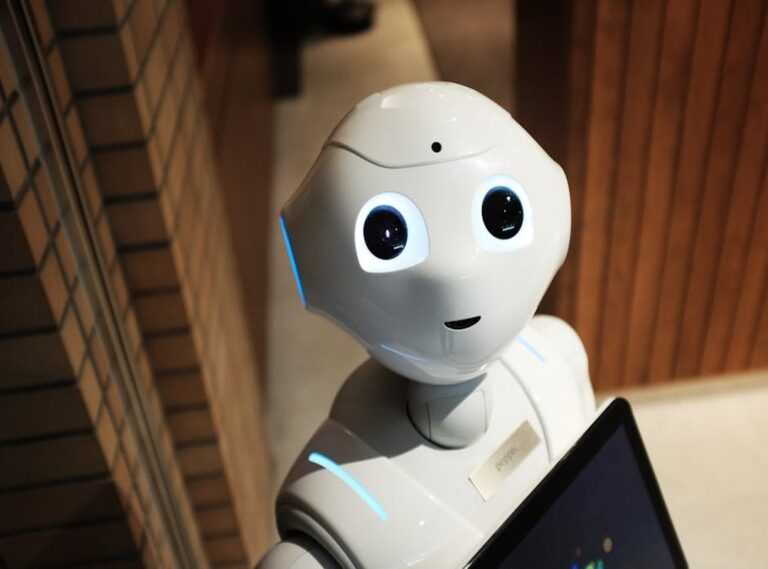
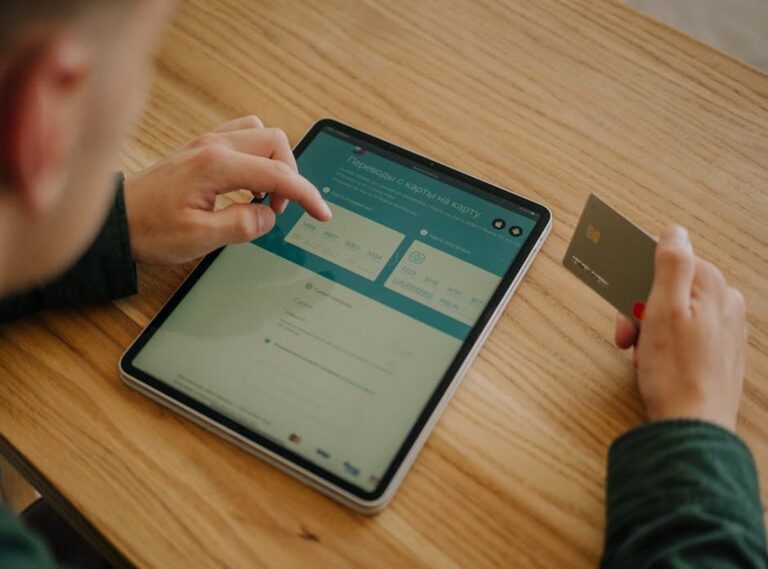
What “Zero Trust” Actually Means Zero Trust sounds dramatic, but it’s actually simple: trust no one, verify everything. Whether it’s a user logging in or a device connecting to your network, nothing gets a free pass not even internal assets. Everyone and everything must prove they belong, continuously. This model is built on a few […]
Zero Trust Security Model Explained with Use Cases Read More »
















![zelda discount for princesses [4k][blacked][aphy3d]](https://thecodecraftershub.com/wp-content/uploads/2025/10/zelda-discount-for-princesses-4kblackedaphy3d-768x511.jpg)